Automated attack bots bombard web apps with malicious requests as soon they go online. Attackers target every website and ecommerce store eventually, hoping to find a vulnerability they can exploit to inject code, misuse resources, or steal data. In 2019, bad bots generated a quarter of all web traffic. cPanel & WHM includes many features that help web hosts and site administrators to repel bad bots, including the ModSecurity web application firewall (WAF).
cPanel & WHM has supported ModSecurity 2 for many years, and in cPanel 92, we introduced support for ModSecurity 3. It should be emphasized that ModSecurity 3 support is experimental, but it offers a couple of significant advantages:
- ModSecurity 3 is faster than earlier versions.
- It does not depend on Apache and can be used with other web servers, including NGINX.
In this article, we’re going to look at what ModSecurity does and how you can install and configure ModSecurity 3 on cPanel & WHM.
What Is Apache ModSecurity and How Does It Work?
Contents
ModSecurity is a web application firewall. It monitors incoming web traffic for threats in real-time, blocking malicious connections before they reach applications. ModSecurity is a rule-based firewall; it compares requests to a list of rules, looking for patterns that match attacks such as SQL injection, session hijacking, cross-site scripting, and more.
Rules are typically provided as a rule set created by a third party, although users can add their own. The Open Web Application Security Project® (OWASP) Core Rule Set is the most widely used. It includes rules that protect web apps against a wide range of threats, including the OWASP Top Ten, a regularly updated list of the most common attacks.
You may be wondering how web-application firewalls differ from the network firewall your server already has. Do you need both? Network firewalls protect servers from malicious traffic at the network layer, as discussed in How To Survive a DDoS Attack, which explains how to install and configure the Config Server Security Firewall (CSF) with cPanel & WHM.
Network firewalls like CSF can’t filter attacks against web applications because they look like legitimate web requests. In contrast, WAFs are specialized to work at the application layer, identifying potentially harmful HTTP requests. If you host web apps on your cPanel server, it’s a good idea to use both a network firewall like CSF and a WAF like ModSecurity.
How to Install ModSecurity in cPanel
To install ModSecurity 3, you will need root access to your server, both on the command line with SSH and in WHM. Because ModSecurity 3 support is experimental, you must first install the EasyApache4 experimental repository.
Log in to your server with SSH and run the following command:
yum install ea4-experimental
Next, we’ll install the connector that allows ModSecurity to work with a web server. We provide two connectors, one for Apache and one for NGINX. They can be installed in the shell or WHM.
First, you’ll need to uninstall ModSecurity 2:
yum remove ea-apache24-mod_security2In the shell, install the relevant connector with one of:
yum install ea-modsec30-connector-apache24 yum install ea-modsec30-connector-nginxIn WHM:
- Navigate to the EasyApache4 page, which you will find in the Software section of the sidebar menu.
- Click Customize under Currently Installed Packages.
- Select the Additional Packages tab.
- Click the switch next to modsec30-connector-apache24 or modsec30-connector-nginx
- Select the Review tab, and click the Provision button at the bottom of the page.
cPanel will now install the connector and its dependencies.
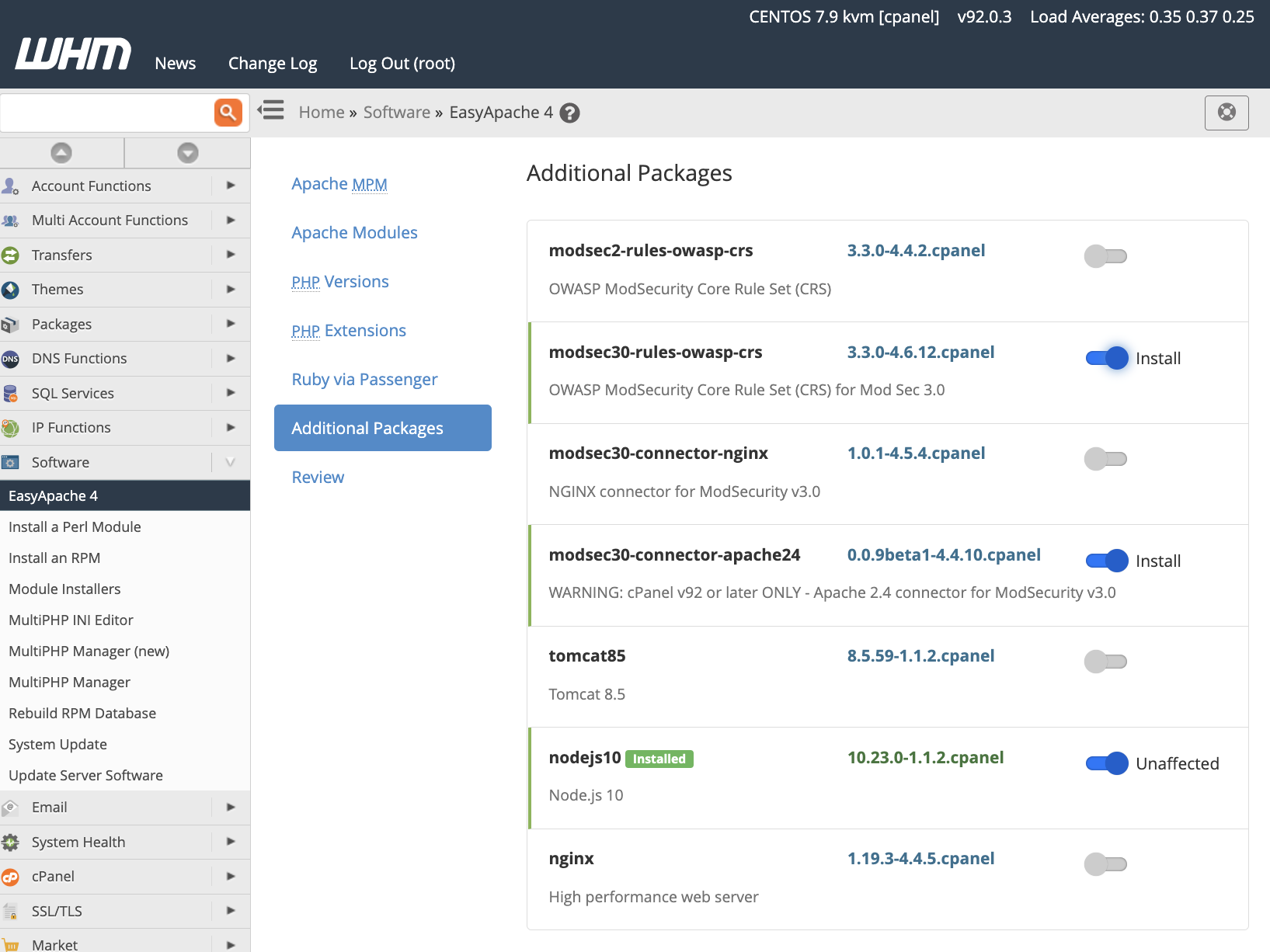
Finally, we’ll install the OWASP Core Rule Set, which you can do in WHM, following the same process as above to install the modsec30-rules-owasp-crs package. You can also install the RPM in the shell with:
yum install ea-modsec30-rules-owasp-crsConfiguring ModSecurity
We have chosen sensible defaults that should work in most web hosting scenarios, but we also provide tools for configuring ModSecurity and its rules in WHM’s Security Center.
ModSecurity Configuration
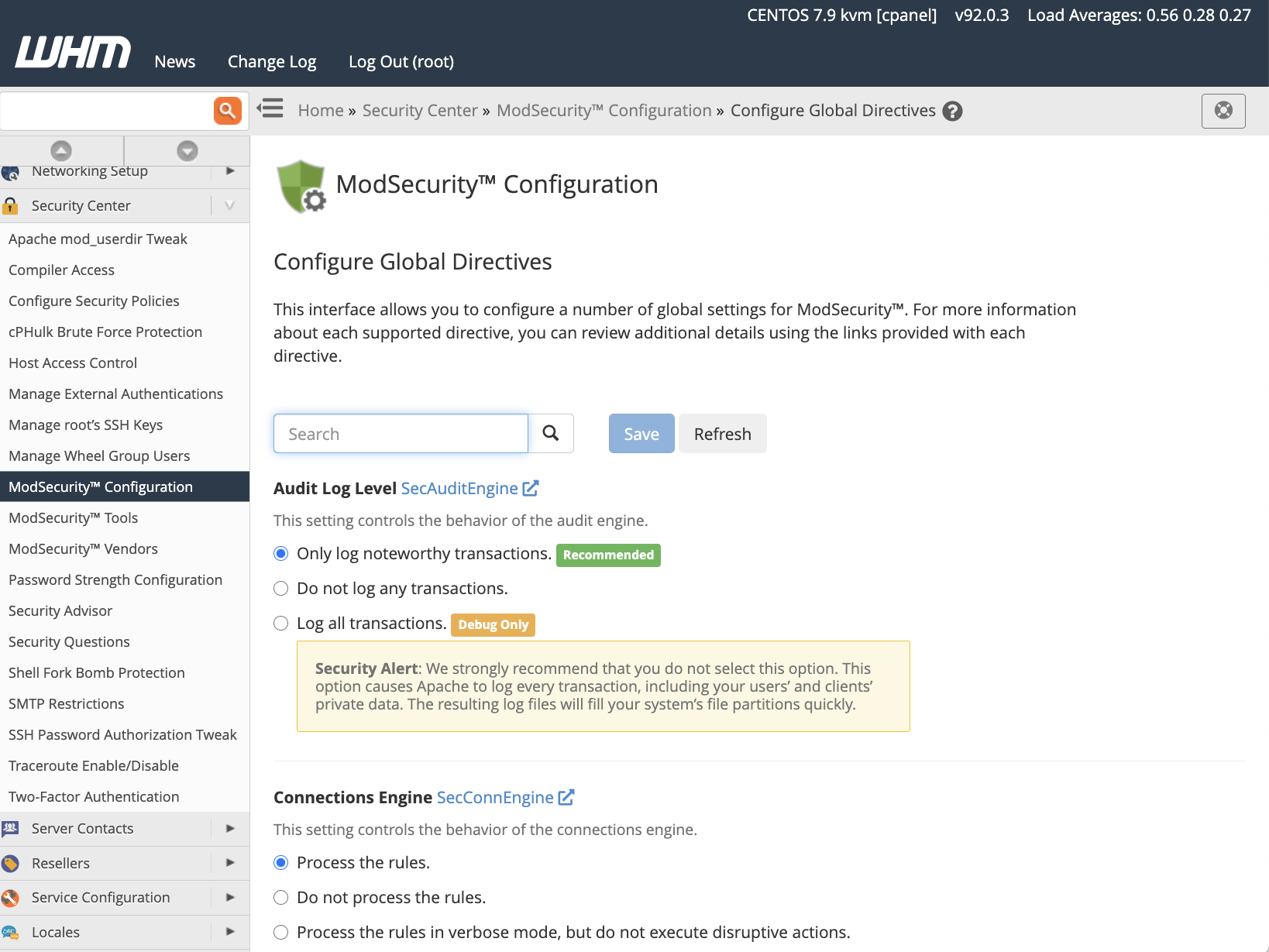
ModSecurity Configuration includes settings to control the behavior of various ModSecurity components, including the audit engine, rules engine, and connection engine. If you would like to use an external geolocation database or logging tool, you can configure the relevant paths and binaries in this interface too.
To learn more about these configuration options, see our ModSecurity Configuration documentation.
ModSecurity Tools
ModSecurity Tools is the primary interface for monitoring and configuring the firewall’s rules. The Hits List displays requests that triggered a rule and allows users to deactivate rules if they want to enable similar connections in the future.
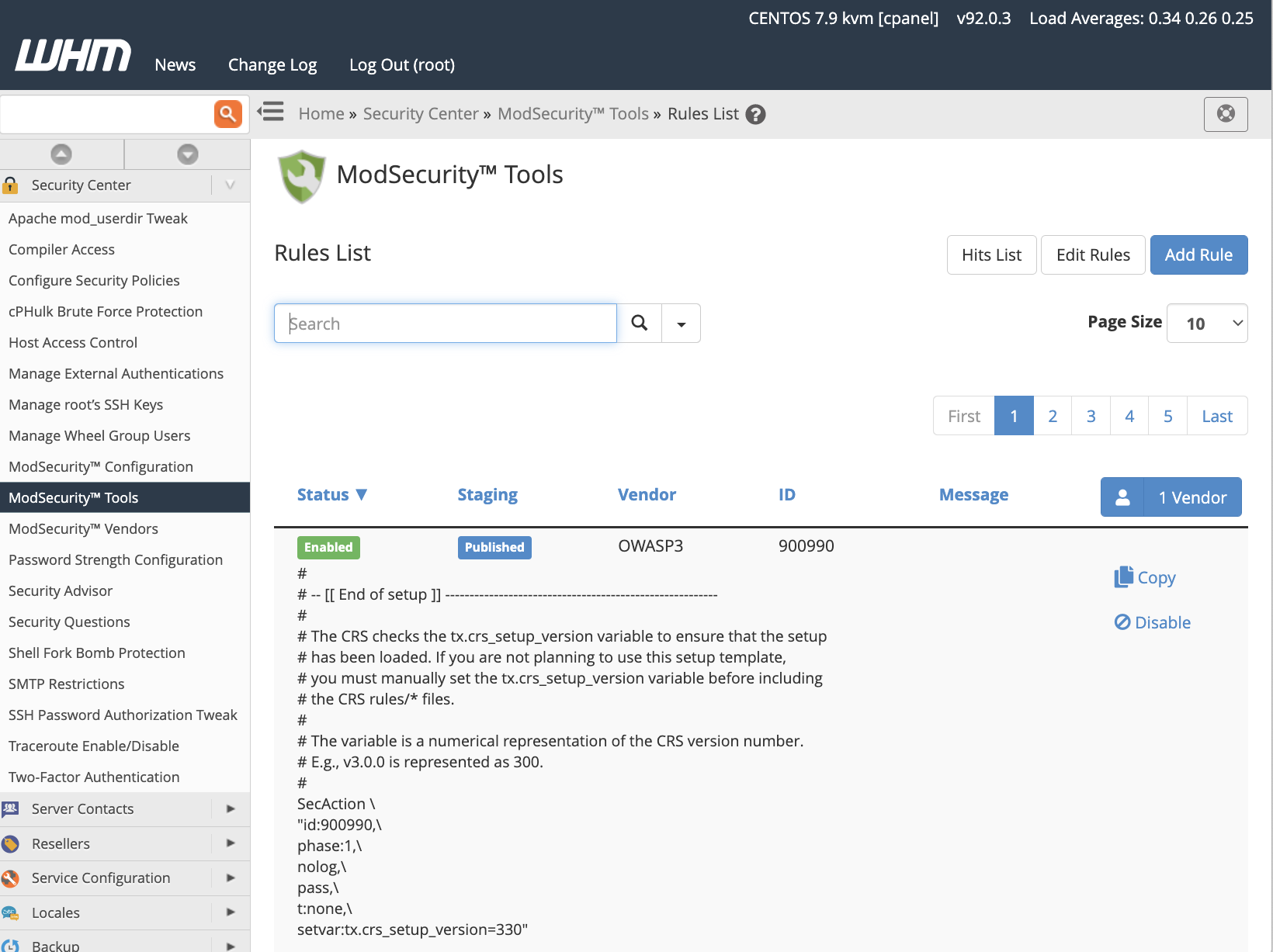
ModSecurity Tools also provides an interface for viewing rules and their status, editing them, and adding new rules using ModSecurity’s SecRules language.
ModSecurity Vendors
ModSecurity Vendors includes tools for adding and managing rule sets. If you followed the instructions in the previous section, you should see the cPanel-provided OWASP CRS rule set, which you can activate or deactivate here, as well as controlling automatic updating. You can also turn on and off groups of rules in the rule set, such as IP reputation, WordPress® exclusion, and scanner detection rules.
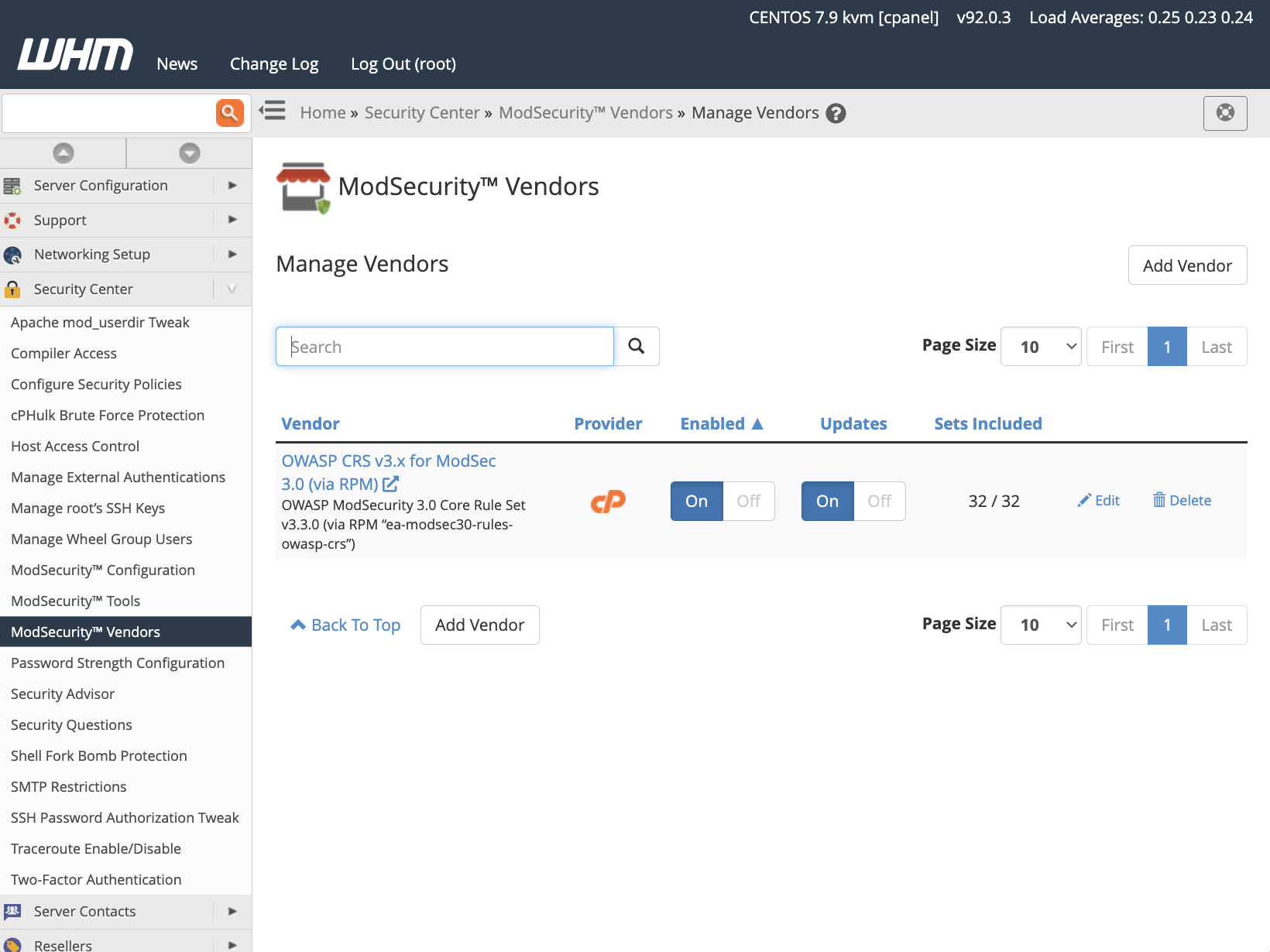
Hosting providers may prefer to create a bespoke rule set or purchase one from a third-party vendor. ModSecurity Vendors also includes features for adding and managing third-party rulesets.
Users who would rather configure ModSecurity 3 via its configuration files will find more information in our ModSecurity 3 documentation.
Managing ModSecurity with ModSecurity SDBM utility
ModSecurity stores details about IPs and requests in the /var/cpanel/secdatadir/ip.pag file. Over time, this file may consume excessive disk space because ModSecurity doesn’t purge stale data. If you would like the system to automatically clean this cache, install the ModSecurity SDBM utility with:
yum install ea-modsec-sdbm-utilcPanel’s maintenance scripts will trigger the utility automatically if it’s installed, but you can also run it manually with the following command:
/scripts/shrink_modsec_ip_database -xAs a general rule, we advise system administrators to let the maintenance scripts handle cache clean-ups. If you do decide to run the SDBM tool utility manually, be sure to restart Apache with:
/scripts/restartsrv_httpdModSecurity 3, cPanel, and NGINX
Unlike earlier versions, ModSecurity 3 is a standalone tool that works independently of the webserver. It no longer depends on Apache and can be integrated with NGINX on cPanel via EasyApache4’s ea-modsec30-connector-nginx connector.
However, NGINX support on cPanel is experimental, and we advise against using it as an Apache replacement for production sites. Although we are working on it, NGINX is not yet a standalone alternative to Apache on cPanel servers, as we explain in How to Install and Manage NGINX on cPanel.
We’re committed to simplifying and automating web site and app hosting, including security configuration. With cPanel & WHM, it’s straightforward to install and manage ModSecurity 3, a fast, powerful web application firewall that protects applications from a huge range of attacks and vulnerabilities.
As always, if you have any feedback or comments, please let us know. We are here to help in the best ways we can. You’ll find us on Discord, the cPanel forums, and Reddit.



